Introduction
A groundbreaking cyber vulnerability has just been disclosed by researchers from ETH Zürich and Google Security. The new Phoenix RowHammer Attack (CVE-2025-6202, CVSS Score: 7.1) targets DDR5 memory chips from SK Hynix, one of the leading DRAM manufacturers. By exploiting weaknesses in DDR5 protections, attackers can achieve privilege escalation to root level in as little as 109 seconds.
This makes Phoenix the first-ever RowHammer privilege escalation exploit affecting production-grade DDR5 systems with default security settings. The implications for hardware security, cloud computing, and cryptographic protection are significant.
🔎 What is the Phoenix RowHammer Attack?
RowHammer is a hardware-level vulnerability discovered in 2014. When a memory row in a DRAM module is accessed (or “hammered”) excessively, it can cause bit flips in adjacent rows, leading to data corruption.
The Phoenix attack builds on this concept but introduces a next-generation hammering pattern that circumvents DDR5’s built-in safety mechanisms such as:
- Target Row Refresh (TRR)
- On-Die Error Correction Code (ECC/ODECC)
Key Findings from the Phoenix Research:
- All 15 DDR5 modules from SK Hynix tested between 2021 and 2024 were found vulnerable.
- Privilege escalation to root was achieved on a Linux desktop in just 109 seconds.
- MITIGATION bypass: on-die ECC and TRR proved insufficient against this new hammering method.
- Exploits are possible against page table entries, RSA-2048 private keys, and local sudo binaries.
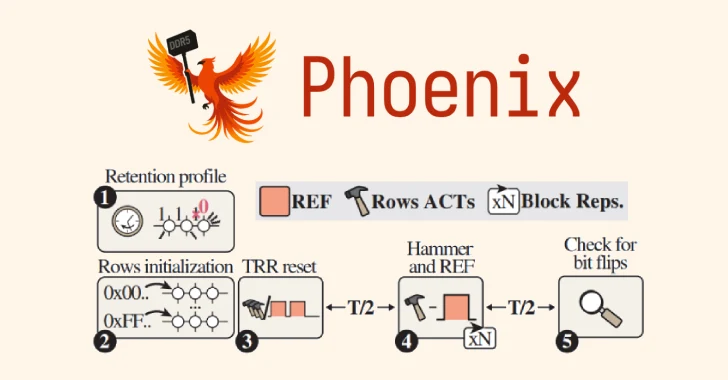
🧩 How Does Phoenix Work?
The research team reverse-engineered DDR5 memory and identified blind spots in TRR refresh intervals. Using this, they developed two entirely new hammering patterns.
✔ Pattern 1 (128 tREFI intervals): Shorter and more effective, tested successfully on 8 DIMMs.
✔ Pattern 2 (2608 tREFI intervals): Longer and slower, but still bypassed security on the remaining DIMMs.
Since the patterns required long execution sequences, the researchers developed self-correcting refresh synchronization. This technique automatically resynchronizes the hammering attack with DDR5’s refresh cycles, allowing thousands of hammering operations without losing alignment.
As a result, Phoenix can consistently flip exploitable bits across DDR5 systems.
🔐 Real-World Exploitation Scenarios
The Phoenix RowHammer attack is not just theoretical—it has practical implications.
- 🚀 Privilege Escalation:
Attackers can exploit flipped bits to escalate privileges, gaining root access on Linux systems. - 🔑 Cryptographic Attacks:
Phoenix can corrupt RSA-2048 keys, breaking SSH authentication in co-located virtual machines. - 🖥️ Memory Manipulation:
By targeting page table entries (PTEs), attackers gain arbitrary read/write memory access. - ⛔ Denial of Service:
Sustained hammering can destabilize systems, leading to crashes and outages.
These attack paths pose risks for data centers, enterprises, cloud providers, and even consumer PCs.

🛡️ Why DDR5 Security Failed
Despite promises of enhanced protection, DDR5 remains vulnerable. Here’s why:
- ECC Limitations: ODECC (On-Die ECC) can correct some random bit flips, but Phoenix exploits accumulative flips over time, bypassing ECC corrections.
- TRR Weakness: Target Row Refresh algorithms fail to sample all refresh intervals consistently, leaving exploitable gaps.
- Scaling Problem: As manufacturers push for greater DRAM density, susceptibility to RowHammer increases.
That means future generations of memory may be even more vulnerable, unless fundamentally new mitigation strategies are developed.
🛠️ How to Mitigate Phoenix RowHammer
Since DDR5 modules cannot be firmware-patched, the Phoenix vulnerability will remain active in deployed systems for years. However, ETH Zürich and Google recommend immediate mitigations:
- Increase Refresh Rate 3x: Researchers found that tripling the refresh rate stopped Phoenix attacks on test systems. This comes with an 8.4% performance penalty.
- BIOS Updates: AMD has reportedly issued a BIOS-level mitigation patch, though independent verification is pending.
- Future Hardware Redesign: DRAM vendors need principled RowHammer defense mechanisms rather than patchwork TRR algorithms.
- Risk-Aware Deployments: Cloud providers should segment workloads and monitor for memory-level anomalies.
📊 Pros and Cons of Phoenix Discovery
✅ Pros (Security Community Benefits)
- Raises awareness about hardware-level vulnerabilities in DDR5.
- Provides a proof-of-concept exploit for researchers and defenders.
- Pushes manufacturers toward designing stronger safeguards.
- Opens doors for academic contributions in memory security research.
❌ Cons (Cybersecurity Risks)
- Attack is now publicly documented, enabling cybercriminal exploitation.
- Existing billions of DDR5 devices cannot be fully protected against Phoenix.
- Performance overhead of mitigations (3x refresh) affects efficiency in servers.
- Undermines trust in ECC and TRR protections.

📢 Industry Impact
The Phoenix vulnerability shakes confidence in DDR5 memory’s security. Its implications extend to:
- Cloud Computing Providers: Risk of cross-tenant attacks in virtualized environments.
- Enterprise Security: Potential root exploits on corporate desktops and servers.
- Consumer Devices: Gaming rigs and personal PCs using DDR5 are also exposed.
- Cryptographic Systems: Secure key storage and encryption services may be undermined.
📰 Related Attacks (RowHammer Variants)
Phoenix follows a long line of RowHammer exploits, each bypassing defenses:
- TRRespass (2020): Bypassed TRR in DDR4.
- Half-Double (2021): Showed bit flips two rows away.
- Blacksmith (2021): Broke DDR4 protections.
- ECC.fail (2024): First successful end-to-end RowHammer exploit against ECC servers.
- OneFlip (2025): Manipulated DNN model weights for AI backdoors.
Phoenix, however, is the first major DDR5 RowHammer exploit with full root privilege escalation.
🔮 Future of DRAM Security
With Phoenix proving DDR5’s vulnerability, the future of DRAM security must evolve. The researchers emphasize that:
- Security needs principle-based designs, not just incremental fixes.
- Stronger memory controllers & firmware-level solutions are required.
- Longer-term investments in novel memory architectures could eliminate RowHammer class attacks.
For now, providers and enterprises must balance performance trade-offs against the urgent need for security.
⚡ Conclusion
The Phoenix RowHammer Attack represents a turning point in memory security. Despite advancements in DDR5, ETH Zürich and Google have proven that RowHammer is alive and well—and now more dangerous than ever.
With privilege escalation possible in under two minutes, the Phoenix exploit raises urgent questions for system administrators, enterprises, and hardware vendors alike. While tripling refresh rates offers a short-term solution, the long-term fix will demand new approaches to memory design.
As DRAM becomes denser and systems more dependent on DDR5, these vulnerabilities must be addressed, or we risk ushering in an era where hardware-level exploits bypass even the strongest software defenses.



